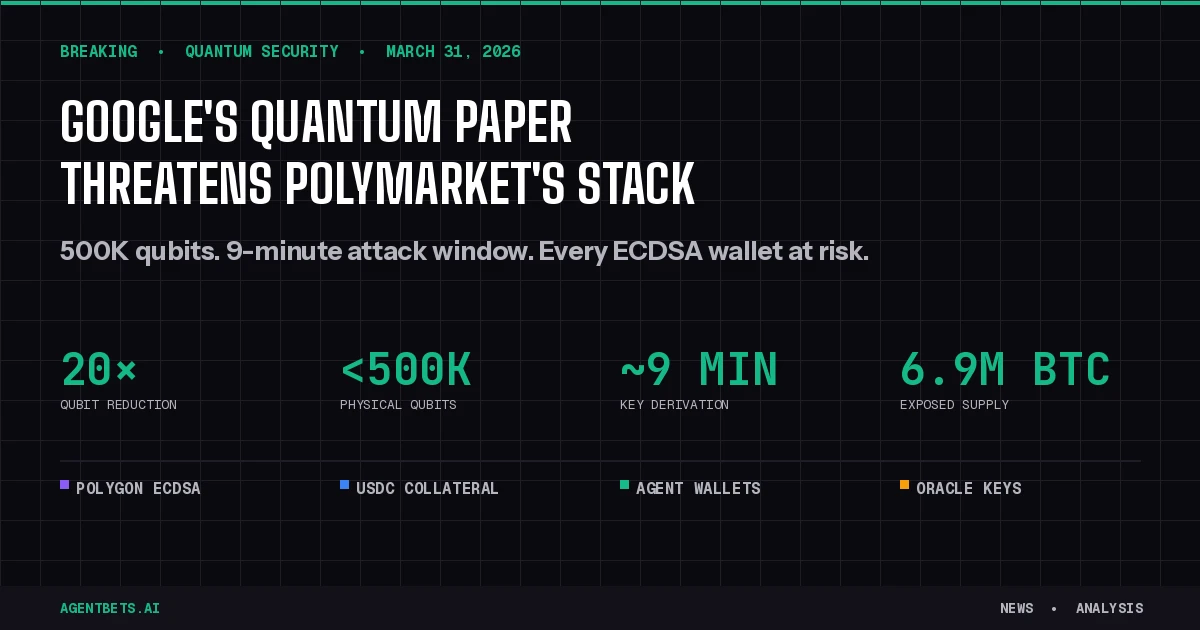
Google Quantum AI published a whitepaper on March 31, 2026 showing that cracking the elliptic curve cryptography securing Bitcoin and Ethereum wallets could require fewer than 500,000 physical qubits — a 20x reduction from prior estimates. The implications ripple directly into Polymarket’s settlement layer, wallet infrastructure, USDC collateral, and the autonomous agents trading on it.
What Google Actually Published
The paper targets ECDLP-256, the specific elliptic curve problem that secures virtually every crypto wallet on Ethereum, Polygon, and Bitcoin. Previous estimates placed the qubit requirement for breaking ECDLP-256 in the millions. Google’s team designed two optimized attack implementations using Shor’s algorithm, each requiring roughly 1,200 to 1,450 high-quality logical qubits and fewer than 500,000 physical qubits total.
The research was co-authored with Ethereum Foundation researcher Justin Drake and Stanford cryptographer Dan Boneh. In a first for quantum cryptanalysis, the team withheld attack circuit details and instead published a zero-knowledge proof allowing third-party verification without exposing a working blueprint.
Google described two distinct attack categories:
| Attack Type | Target | Estimated Time | Condition |
|---|---|---|---|
| On-spend | Unconfirmed transactions in mempool | ~9 minutes | Public key exposed during broadcast |
| At-rest | Wallets with permanently exposed public keys | Days to weeks | Key previously revealed on-chain |
The nine-minute on-spend window is significant because Bitcoin’s average block confirmation takes approximately 10 minutes — meaning a sufficiently powerful quantum attacker could beat confirmation roughly 41% of the time.
Google estimated that approximately 6.9 million BTC already sit in wallets with exposed public keys, including 1.7 million coins from the Satoshi era.
Why Polymarket Is Directly Exposed
Polymarket’s entire stack sits on infrastructure this paper explicitly targets. Every layer of the platform relies on the same ECDSA cryptography that Google’s paper calls into question.
Settlement Layer: Polygon and ECDSA
Polymarket settles trades on Polygon, an Ethereum Layer 2 network. Every Polymarket wallet is secured by ECDSA signatures — the exact primitive Google’s paper demonstrates can be cracked with fewer resources than previously believed. User proxy wallets (1-of-1 multisigs deployed to Polygon) hold both ERC-1155 position tokens and USDC.e collateral.
Polygon inherits Ethereum’s cryptographic assumptions. When Ethereum migrates to post-quantum signatures, Polygon must follow — but L2s historically lag L1 upgrades by months or years.
Collateral: USDC Exposure
Polymarket currently uses Bridged USDC (USDC.e) on Polygon, with a planned migration to native USDC issued by Circle’s regulated affiliates. Both USDC variants are ERC-20 tokens controlled by standard Ethereum key pairs. A quantum attacker who derives a wallet’s private key gains access to all USDC held in that wallet — not just prediction market positions, but the underlying dollar-denominated collateral.
The platform’s CLOB architecture means that market makers routinely hold significant USDC balances in hot wallets to provide liquidity. These wallets transact frequently, repeatedly exposing public keys on-chain.
Hybrid Architecture Timing Risk
Polymarket’s hybrid off-chain/on-chain design — where orders match instantly off-chain but settle on Polygon with a multi-second delay — already faces documented timing exploits. Quantum threats would compound this: an attacker could theoretically derive keys from transactions visible in the mempool before on-chain settlement completes.
Ethereum’s 12-second slot time provides less attack surface than Bitcoin’s 10-minute blocks, and Polygon confirms even faster. But at-rest attacks (targeting wallets with previously exposed keys) are not constrained by block timing at all. Google estimated the top 1,000 highest-value exposed Ethereum wallets — holding approximately 20.5 million ETH — could be compromised in under nine days.
The Agent Wallet Problem
Over 30% of Polymarket wallets are now operated by AI agents, according to LayerHub analytics. This concentration creates a distinct quantum risk profile:
High-frequency key exposure. Autonomous trading agents execute thousands of transactions, each one exposing the wallet’s public key. The Olas Polystrat agent alone executed over 4,200 trades in a single month. Every trade is a data point a future quantum attacker could target.
Concentrated balances. Agent wallets tend to hold larger USDC balances than retail wallets because they need capital for automated market-making and arbitrage strategies. A single compromised agent wallet could represent significant losses.
Key management complexity. Most agent architectures described in the agent wallet security guide rely on MPC, session keys, or TEE-based signing — all of which ultimately depend on ECDSA key pairs that quantum computers could break. Post-quantum migration for agent wallets requires upgrading not just the wallet primitive but the entire signing pipeline.
No human in the loop. Agent wallets that automatically approve transactions cannot pause for manual verification of quantum-suspicious activity. The agent betting stack’s wallet layer (Layer 2) will need quantum-aware circuit breakers.
Prediction Markets on Quantum Computing Itself
The irony is thick: Polymarket already hosts 104 active quantum computing prediction markets. Traders are betting on the timeline and impact of the very technology that threatens the platform’s infrastructure.
These markets now function as self-referential risk indicators. If prediction market consensus shifts toward earlier Q-Day estimates, the rational response is to reduce exposure to the very platform pricing that risk — creating a potential reflexive feedback loop where quantum fear undermines confidence in the quantum-betting venue itself.
Markets like “Will Bitcoin replace SHA-256 before 2027?” take on new urgency when the paper’s co-author Justin Drake publicly stated his confidence in Q-Day by 2032 has increased significantly and estimated at least a 10% probability that a quantum computer recovers a private key from an exposed public key by that date.
What Ethereum’s Roadmap Means for Polymarket
The timeline for post-quantum protection depends almost entirely on Ethereum’s upgrade schedule. Vitalik Buterin published a quantum resistance roadmap on February 26, 2026, identifying four vulnerable components: consensus-layer BLS signatures, KZG commitments in data availability, EOA ECDSA signatures, and application-layer ZK proofs.
The Ethereum Foundation’s Strawmap targets approximately seven forks over four years, with the first two upgrades (Glamsterdam and Hegotá) scheduled for 2026. The Foundation launched pq.ethereum.org in March 2026 as a coordination hub, with over 10 client teams running weekly post-quantum interoperability devnets.
Key milestones for Polymarket:
EIP-8141 (account abstraction for signatures). This proposal would let Ethereum wallets switch signature algorithms — including to quantum-safe schemes — without changing addresses. For Polymarket’s proxy wallet architecture, this is the critical upgrade path.
Hash-based signature migration. Buterin proposed replacing BLS signatures with hash-based variants (Winternitz schemes) and using STARK-based aggregation. Hash-based signatures are significantly larger than ECDSA signatures, which will increase on-chain data costs for high-frequency trading platforms like Polymarket.
Polygon L2 lag. Even after Ethereum L1 adopts post-quantum signatures, Polygon must implement corresponding changes. Polymarket’s migration depends not just on Ethereum’s timeline but on Polygon’s ability to track it. Buterin himself noted that Ethereum could achieve “quantum resistant slots” before “quantum resistant finality” — meaning the chain keeps producing blocks but finality guarantees could be temporarily weakened.
Five Angles Every Prediction Market Trader Should Consider
1. Collateral Security ≠ Market Security
Even if Polymarket’s smart contracts are flawless, the underlying wallet cryptography secures all value on the platform. A quantum attack would not exploit a smart contract bug — it would derive private keys directly, bypassing all contract logic. This is a cryptographic layer below anything Polymarket can fix with a platform update.
2. The Bridge Risk Multiplier
Polymarket’s current USDC.e is bridged USDC — tokens that crossed from Ethereum L1 to Polygon via a bridge contract. Bridge contracts are themselves secured by key pairs. A quantum attack on bridge validator keys could compromise not just individual wallets but the entire bridged asset pool. The planned migration to native USDC (issued directly on Polygon by Circle) partially mitigates this by removing the bridge dependency.
3. Oracle Vulnerability
Polymarket uses UMA’s optimistic oracle for market resolution, where proposers post USDC bonds and outcomes are challenged via tokenholder votes. Both the proposer’s wallet and UMA tokenholders’ wallets are ECDSA-secured. A quantum attacker who compromises enough UMA tokenholder keys could manipulate market resolution — a governance attack vector that compounds the financial one.
4. Regulatory Catalyst
Google’s paper lands as prediction markets face increasing state-level regulatory scrutiny. Regulators already questioning whether platforms like Polymarket offer adequate consumer protection now have a new vector: can a platform be considered “secure” when its underlying cryptography has a published, accelerated obsolescence timeline? This could accelerate demands for post-quantum compliance as a licensing condition.
5. Competitive Moat for Regulated Alternatives
Kalshi, as a CFTC-regulated exchange using traditional financial infrastructure alongside crypto rails, could frame quantum resistance as a differentiator against crypto-native competitors. If Kalshi migrates to post-quantum authentication faster than Polymarket, it gains a security narrative advantage — particularly with institutional participants evaluating cross-platform arbitrage counterparty risk.
What Happens Between Now and Q-Day
The paper’s authors are explicit: quantum computers cannot break real-world wallets today. The largest quantum processors currently operate with far fewer qubits than the 500,000 physical qubit threshold estimated in the paper. Google has pointed to 2029 as a potential milestone for useful quantum systems.
But the security model for crypto has always been forward-looking. Funds deposited today into a Polymarket wallet may still be in that wallet when quantum computers reach the relevant threshold. The “harvest now, decrypt later” attack — where adversaries record encrypted data today and crack it once quantum hardware matures — applies to every on-chain transaction with an exposed public key.
For agent builders, the practical timeline looks like this:
| Milestone | Estimated Date | Impact on Polymarket Agents |
|---|---|---|
| Ethereum Glamsterdam fork | 2026 | May include early PQ signature support |
| Circle native USDC on Polygon | 2026 | Reduces bridge attack surface |
| EIP-8141 deployment | 2026–2027 | Enables wallet signature algorithm migration |
| Ethereum full PQ finality | 2028–2030 | ECDSA fully deprecated |
| Google quantum milestone | ~2029 | Theoretical attack feasibility |
The gap between “theoretical attack feasibility” and “Ethereum full PQ finality” is the window of maximum risk. Polymarket’s security posture during that window depends on Ethereum’s ability to ship post-quantum upgrades faster than quantum hardware scales.
The Bottom Line for Agent Builders
Google’s paper does not mean Polymarket wallets are compromised today. It means the timeline for when they could be is shorter and the resource bar is lower than the industry assumed. For anyone building or operating autonomous agents on prediction markets, the action items are concrete: monitor Ethereum’s PQ upgrade timeline, evaluate wallet architectures that can swap signature schemes, avoid unnecessary public key exposure through address reuse, and build migration plans into agent infrastructure now — not when the first qubit-scale quantum processor ships.
The prediction market that prices quantum risk most accurately may be the one that takes the longest to protect itself from it.